Ensuring Data Privacy
At Axiata, data privacy is a core element of our commitment to building a trusted digital ecosystems. We safeguard personal data through a comprehensive framework aligned with national laws and global best practices, while fostering transparency, accountability, and user empowerment across all operations.




Commitment to Data Privacy: Data Privacy Notice
We are committed to protecting the privacy and personal data of our customers, employees, and stakeholders with the highest levels of respect and care. Our overarching Data Privacy Policy establishes the mandatory requirements for all Axiata Group entities regarding the protection and responsible handling of personal data.
At the core of this Policy is the belief that good privacy is good business. It is a vital part of corporate governance and accountability, enabling trust in digital interactions. By adopting strong privacy practices, Axiata reinforces its commitment to digital ethics and strengthens customer confidence across our markets.
Our Privacy Commitment: The T.R.U.S.T. Principles
Our data privacy program is anchored on the T.R.U.S.T. principles, which guide every interaction, process, and system where personal data is involved.
We are TRANSPARENT about what, why, and how we collect and protect YOUR PERSONAL DATA so that YOU can make informed decisions.
We respect YOUR RIGHTS as individuals, so YOU are in control of YOUR PERSONAL DATA.
We USE YOUR PERSONAL DATA for specific and stated purposes and keep it for as long as required only.
We have established robust CYBER SECURITY PRACTICES in line with leading industry standards to protect YOUR PERSONAL DATA that YOU have shared with us.
With YOUR CONSENT or in accordance with APPLICABLE LAWS we may TRANSFER YOUR PERSONAL DATA and will take appropriate steps to ensure it is adequately protected.
Data Privacy Governance and Risk Oversight
Axiata’s Data Privacy Strategy is governed by the Operational layer, management layer, and board level, ensuring data privacy is fully integrated into how we operate, innovate, and protect trust.
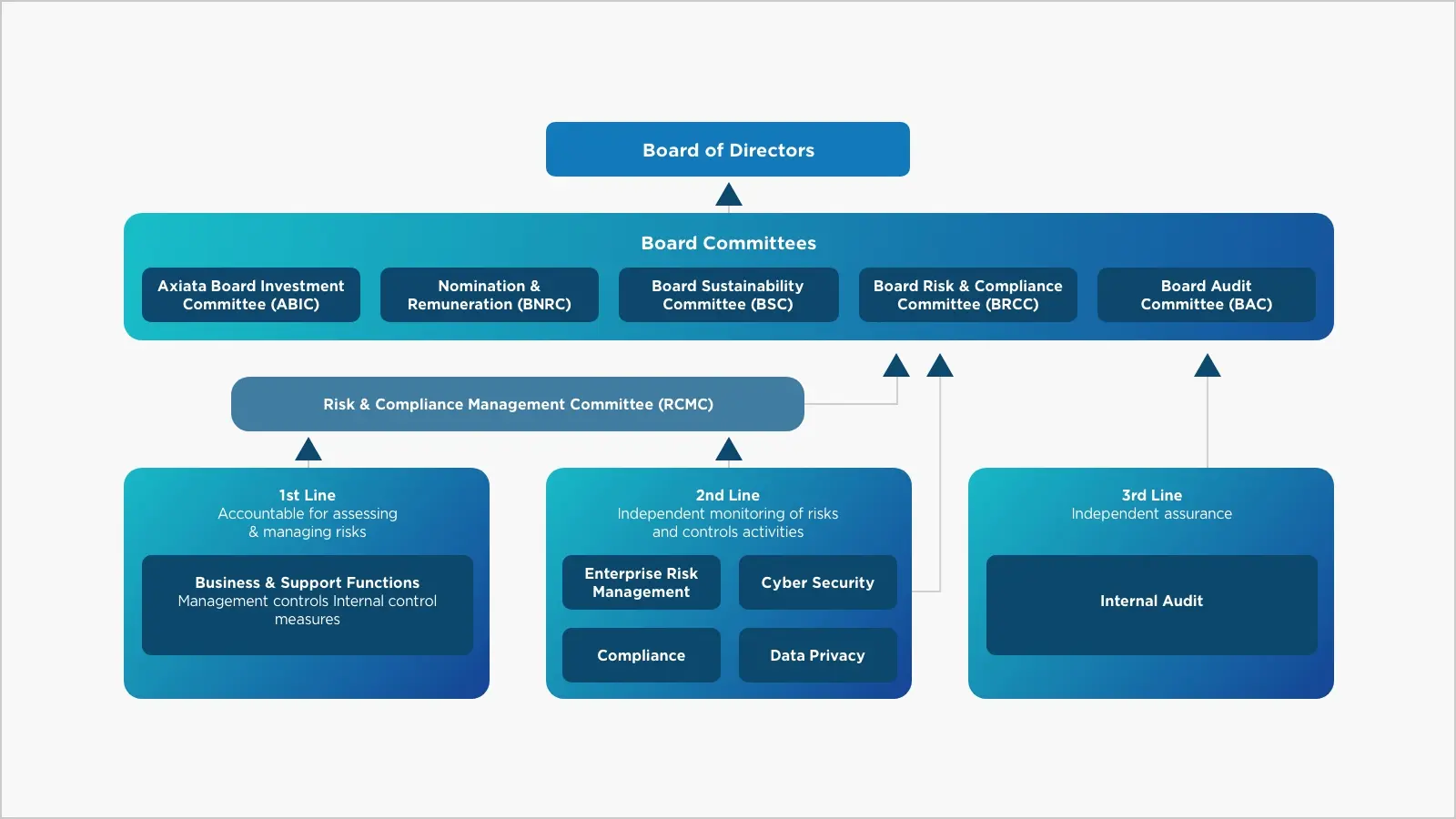
Oversight of the Data Privacy risk management, provides direction on policies and frameworks to address risk and compliance, reviews and articulates strategic emerging and inherent risks, and ensures sufficient implementation plans are formulated to mitigate risk exposure.
The RCMC is responsible for determining that there are robust processes in place for identifying, assessing, and monitoring amongst others, key business risks to safeguard the Company’s assets; and risks relating to data privacy.
The three lines of defense model ensures effective control implementation, management assurance, and independent validation.
Ensures strategic clarity, compliance assurance, and operational agility across all OpCos.
Charting Our Data Privacy Journey
At Axiata, we have built a strong, forward-looking Data Privacy program that supports our digital ambitions while protecting customer trust and regulatory compliance. Key achievements that define our journey:
Built and rolled out a comprehensive privacy governance framework across all operating companies, aligned with international and local regulations to ensure consistent and compliant data handling.
Adopted a CMMI-based maturity model to benchmark and systematically improve privacy capabilities across OpCos, with measurable and sustained growth in maturity levels over time.
Introduced a structured privacy enhancement program (#ASH 3.0) that embedded privacy controls into core business functions, architecture, and risk processes, including breach detection and legitimate interest assessments.
Aligned cybersecurity and privacy controls by integrating them into enterprise risk dashboards and workflows to improve real-time visibility, responsiveness, and breach mitigation effectiveness.
Critical processes and digital assets involved in such processes have been screened against Privacy Enhancing Technologies and risk based implementation journey has been started to ensure digital integrity across the Group
Axiata Measures its Data Privacy maturity over 12 Key Domains
Axiata establishes strong privacy governance through a clear organizational structure, accountability, and leadership oversight. This includes board-level reporting, enterprise-wide privacy roles, and integrated risk and compliance oversight.
We continuously monitor and implement evolving data protection laws across ASEAN and global markets, embedding compliance into our business processes.
Transparent notices and user-centric choice mechanisms are implemented across digital channels to ensure data subjects are informed and empowered.
We govern personal data through its lifecycle—from collection and classification to retention and disposal—ensuring accuracy, integrity, and purpose limitation.
We enable seamless, timely fulfillment of data subject rights including access, correction, erasure, and objection in accordance with legal obligations.
All employees and relevant third parties are trained on privacy principles, risks, and controls. Culture of privacy is driven through continuous awareness campaigns.
Direct marketing activities are conducted with clear consent, opt-out mechanisms, and respect for user preferences, aligned with data protection laws.
Privacy is embedded into the design and operation of systems, processes, and products from the outset, not as an afterthought.
Strong cybersecurity controls protect personal data from unauthorized access, loss, or misuse, aligned with ISO 27001 and industry best practices.
Third-party disclosures follow strict due diligence, legal agreements, and assurance of equivalent data protection standards.
We obtain, record, and manage user consent in an explicit, informed, and granular manner—ensuring traceability and ease of withdrawal.
We maintain robust breach detection, response, and notification procedures that meet regulatory timelines and minimize user impact.
Commitment to Data Privacy: Data Privacy Notice
We are committed to protecting the privacy and personal data of our customers, employees, and stakeholders with the highest levels of respect and care. Our overarching Data Privacy Policy establishes the mandatory requirements for all Axiata Group entities regarding the protection and responsible handling of personal data.
At the core of this Policy is the belief that good privacy is good business. It is a vital part of corporate governance and accountability, enabling trust in digital interactions. By adopting strong privacy practices, Axiata reinforces its commitment to digital ethics and strengthens customer confidence across our markets.
Our Privacy Commitment: The T.R.U.S.T. Principles
Our data privacy program is anchored on the T.R.U.S.T. principles, which guide every interaction, process, and system where personal data is involved.
We are TRANSPARENT about what, why, and how we collect and protect YOUR PERSONAL DATA so that YOU can make informed decisions.
We respect YOUR RIGHTS as individuals, so YOU are in control of YOUR PERSONAL DATA.
We USE YOUR PERSONAL DATA for specific and stated purposes and keep it for as long as required only.
We have established robust CYBER SECURITY PRACTICES in line with leading industry standards to protect YOUR PERSONAL DATA that YOU have shared with us.
With YOUR CONSENT or in accordance with APPLICABLE LAWS we may TRANSFER YOUR PERSONAL DATA and will take appropriate steps to ensure it is adequately protected.
Data Privacy Governance and Risk Oversight
Axiata’s Data Privacy Strategy is governed by the Operational layer, management layer, and board level, ensuring data privacy is fully integrated into how we operate, innovate, and protect trust.
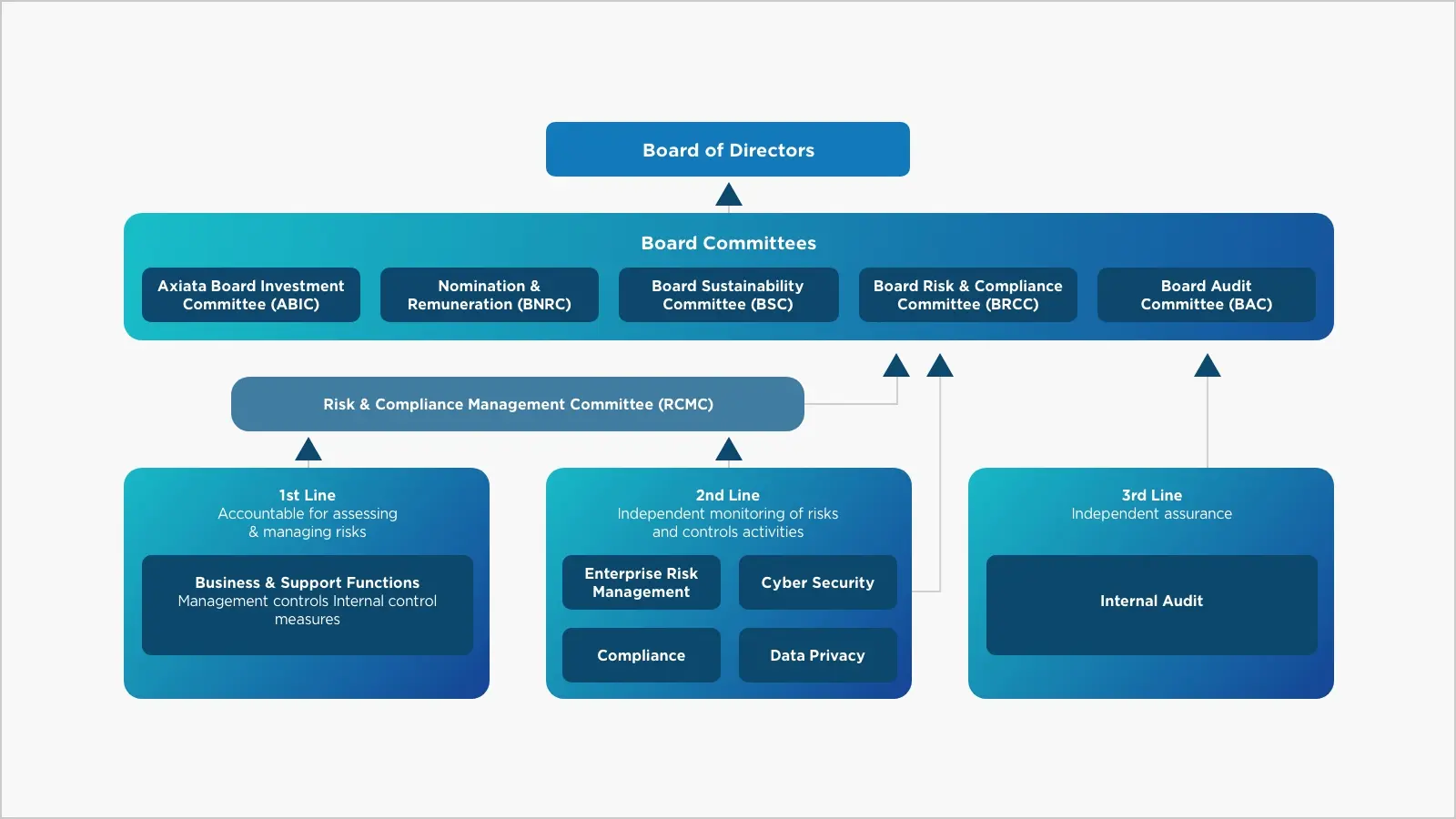
Oversight of the Data Privacy risk management, provides direction on policies and frameworks to address risk and compliance, reviews and articulates strategic emerging and inherent risks, and ensures sufficient implementation plans are formulated to mitigate risk exposure.
The RCMC is responsible for determining that there are robust processes in place for identifying, assessing, and monitoring amongst others, key business risks to safeguard the Company’s assets; and risks relating to data privacy.
The three lines of defense model ensures effective control implementation, management assurance, and independent validation.
Ensures strategic clarity, compliance assurance, and operational agility across all OpCos.
Charting Our Data Privacy Journey
At Axiata, we have built a strong, forward-looking Data Privacy program that supports our digital ambitions while protecting customer trust and regulatory compliance. Key achievements that define our journey:
Built and rolled out a comprehensive privacy governance framework across all operating companies, aligned with international and local regulations to ensure consistent and compliant data handling.
Adopted a CMMI-based maturity model to benchmark and systematically improve privacy capabilities across OpCos, with measurable and sustained growth in maturity levels over time.
Introduced a structured privacy enhancement program (#ASH 3.0) that embedded privacy controls into core business functions, architecture, and risk processes, including breach detection and legitimate interest assessments.
Aligned cybersecurity and privacy controls by integrating them into enterprise risk dashboards and workflows to improve real-time visibility, responsiveness, and breach mitigation effectiveness.
Critical processes and digital assets involved in such processes have been screened against Privacy Enhancing Technologies and risk based implementation journey has been started to ensure digital integrity across the Group
Axiata Measures its Data Privacy maturity over 12 Key Domains
Axiata establishes strong privacy governance through a clear organizational structure, accountability, and leadership oversight. This includes board-level reporting, enterprise-wide privacy roles, and integrated risk and compliance oversight.
We continuously monitor and implement evolving data protection laws across ASEAN and global markets, embedding compliance into our business processes.
Transparent notices and user-centric choice mechanisms are implemented across digital channels to ensure data subjects are informed and empowered.
We govern personal data through its lifecycle—from collection and classification to retention and disposal—ensuring accuracy, integrity, and purpose limitation.
We enable seamless, timely fulfillment of data subject rights including access, correction, erasure, and objection in accordance with legal obligations.
All employees and relevant third parties are trained on privacy principles, risks, and controls. Culture of privacy is driven through continuous awareness campaigns.
Direct marketing activities are conducted with clear consent, opt-out mechanisms, and respect for user preferences, aligned with data protection laws.
Privacy is embedded into the design and operation of systems, processes, and products from the outset, not as an afterthought.
Strong cybersecurity controls protect personal data from unauthorized access, loss, or misuse, aligned with ISO 27001 and industry best practices.
Third-party disclosures follow strict due diligence, legal agreements, and assurance of equivalent data protection standards.
We obtain, record, and manage user consent in an explicit, informed, and granular manner—ensuring traceability and ease of withdrawal.
We maintain robust breach detection, response, and notification procedures that meet regulatory timelines and minimize user impact.
Please share your details, and we’ll be in touch shortly.